Complete guide to UDP proxy architecture, port handling, and UDP vs TCP IP comparisons—plus enterprise static residential UDP solutions.
In the layered ecosystem of network infrastructure, proxies serve as the silent gatekeepers of data flow. While most professionals are familiar with HTTP/HTTPS proxies operating over TCP, the UDP proxy remains an underappreciated yet critical component for high-performance applications. Understanding its mechanics—from UDP port management to the fundamental distinctions of UDP IP vs TCP IP—is essential for architects, developers, and businesses that demand speed, anonymity, and reliability.
To fully appreciate the role of a UDP proxy, we must first establish a precise understanding of what a UDP port is. In the TCP/IP networking model, a port is a 16-bit numerical identifier embedded within the transport layer header. UDP ports serve the same addressing function as TCP ports but operate within the stateless context of the User Datagram Protocol.
Key characteristics of UDP ports:
Common UDP port assignments:
| Port | Service | Purpose |
|---|---|---|
| 53 | DNS | Domain name resolution |
| 67/68 | DHCP | IP address assignment |
| 123 | NTP | Network time synchronization |
| 500 | IPSec/IKE | VPN key exchange |
| 1194 | OpenVPN | VPN tunnel transport |
| 5060 | SIP | VoIP signaling |
| 27015-27030 | Steam/Game Servers | Online gaming traffic |
Understanding what UDP port is not merely academic—it directly impacts how proxy administrators configure firewall rules, load balancers, and routing policies. Every UDP-based application binds to specific ports, and a UDP proxy must be capable of handling traffic across this diverse port spectrum.
The debate of UDP IP vs TCP IP extends far beyond simple "reliable vs. unreliable" characterizations. These protocols represent fundamentally different philosophies of data transmission.
Deep comparison table:
| Feature | TCP IP | UDP IP |
|---|---|---|
| Connection establishment | Three-way handshake (SYN, SYN-ACK, ACK) | No handshake; immediate transmission |
| Header size | 20-60 bytes | 8 bytes |
| Flow control | Window-based sliding window | None |
| Congestion control | Algorithms like Cubic, BBR | None (application must implement) |
| Error recovery | Automatic retransmission | None |
| Packet ordering | Guaranteed sequential delivery | No guarantee |
| Overhead | High | Low |
| Ideal use cases | Web, email, file transfer, databases | VoIP, gaming, streaming, DNS, VPN |
Why latency differs so dramatically:
TCP's reliability mechanisms introduce variable latency. When a packet is lost, TCP pauses subsequent data transmission until the missing segment is retransmitted and acknowledged—a phenomenon known as "head-of-line blocking." UDP suffers no such penalty. In real-time applications, a single lost UDP packet results in a momentary glitch (e.g., a dropped video frame or a split-second audio gap) rather than a prolonged stall.
Click TCP Port and TCP Proxy to get more details about TCP.
UDP IP vs TCP IP in modern architectures: With the rise of HTTP/3 and QUIC (Quick UDP Internet Connections), the line is blurring. QUIC, developed by Google, implements TCP-like reliability and encryption over UDP, combining the speed of UDP with the reliability of TCP. This evolution underscores the growing recognition that UDP's foundation—with its minimal overhead and flexible UDP port handling—is the future of low-latency internet communication.
A UDP proxy is a specialized network intermediary designed to forward User Datagram Protocol traffic between clients and servers. Unlike HTTP proxies that operate at the application layer, UDP proxies function at the transport layer, handling raw datagrams.
Core operational mechanics:
Packet interception: The client is configured to send UDP traffic to the proxy's IP address and designated UDP port rather than directly to the target server.
Session tracking: Because UDP is stateless, the proxy must maintain a session table. Each unique tuple—(source IP, source UDP port, destination IP, destination UDP port, protocol)—is mapped to an upstream connection. This is often called "UDP hole punching" or "flow tracking."
Packet transformation: The proxy may modify packet headers, encapsulate UDP within TCP (for traversing restrictive firewalls), or apply encryption. Common encapsulation protocols include:
Forwarding and response handling: When a response returns from the target server, the proxy consults its session table to determine which original client should receive the packet, then forwards it accordingly.
Types of UDP proxies:
| Type | Description | Use Case |
|---|---|---|
| SOCKS5 Proxy | Supports UDP ASSOCIATE command; handles UDP traffic alongside TCP | General-purpose proxy for gaming, P2P |
| UDP-to-TCP Tunnel | Encapsulates UDP packets inside TCP connections | Corporate networks blocking UDP |
| Load Balancer Proxy | Distributes UDP traffic across multiple backend servers | High-availability DNS, gaming server clusters |
| Residential UDP Proxy | Routes UDP traffic through ISP-assigned residential IPs | Ad verification, streaming, social media automation |
Effective UDP port management distinguishes a well-architected proxy from a poorly performing one. When operating at scale, UDP proxies must handle thousands—or millions—of simultaneous flows.
Key challenges:
Best practices for UDP port handling in proxies:
Modern multiplayer games—from Fortnite and Call of Duty to League of Legends—rely almost exclusively on UDP for gameplay traffic. Game servers send player position, actions, and hit registration via UDP to minimize lag.
Why gaming requires UDP proxy:
Technical requirement: Gaming UDP proxies must support a wide range of UDP ports (often 10,000+) and maintain sub-10ms additional latency to remain viable.
Platforms like Zoom, Microsoft Teams, and WebRTC-based applications use UDP for media transport. SIP signaling often uses UDP port 5060, while RTP (Real-time Transport Protocol) media streams use dynamically allocated high UDP ports.
Proxy benefits for VoIP:
DNS is foundational to internet operations, and DNS queries typically travel over UDP port 53. Proxy solutions are used to:
Modern web scraping increasingly requires handling UDP traffic, particularly for:
Residential UDP proxies are particularly valuable here because they present legitimate consumer IP addresses that ad exchanges and streaming platforms trust.
OpenVPN, WireGuard, and IKEv2/IPSec all utilize UDP as their preferred transport. A UDP proxy can serve as a VPN gateway aggregator, allowing organizations to route VPN traffic through static residential IPs for enhanced anonymity.
When evaluating UDP IP vs TCP IP for anonymity, the protocol choice affects fingerprinting. UDP proxies, especially those using residential IPs, offer distinct advantages:
UDP proxies introduce specific security considerations:
| Risk | Description | Mitigation |
|---|---|---|
| Amplification attacks | Attackers can spoof source IPs to reflect traffic | Implement rate limiting and source IP validation |
| UDP flood | Volumetric DDoS attacks targeting open UDP ports | Deploy upstream DDoS protection; use anycast routing |
| Session hijacking | Stateless nature makes spoofing easier | Implement DTLS encryption between client and proxy |
| Port scanning | Open UDP ports can be enumerated | Use port knocking or authentication before forwarding |
The proxy market offers various IP types—datacenter, mobile, and residential. For UDP applications requiring stability and trust, static residential proxies represent the premium tier.
Comparative analysis:
| Proxy Type | UDP Support | Stability | Block Rate | Use Case |
|---|---|---|---|---|
| Datacenter | Limited | High | High | Non-critical applications |
| Rotating Residential | Variable | Low (IP changes) | Low | Short-term tasks |
| Static Residential | Full | High | Very Low | Long-term sessions, account management, streaming |
Static residential proxies maintain the same IP address over extended periods. This is critical for UDP applications because:
For enterprises and advanced users seeking a robust solution, MoMo Static Residential Proxies supports UDP port across its entire infrastructure.
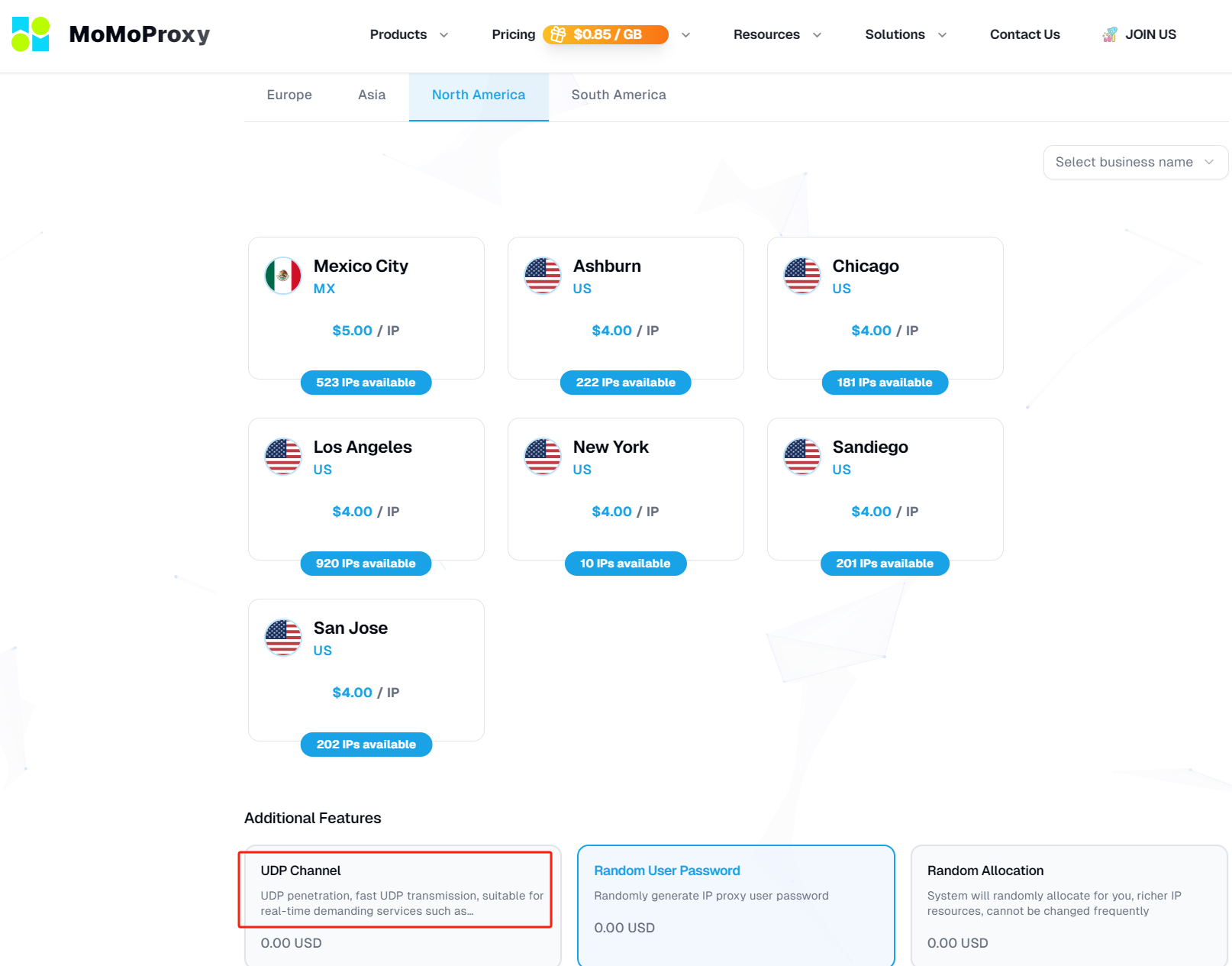
This capability enables:
Technical implementation: MoMo achieves UDP support through optimized SOCKS5 infrastructure with UDP ASSOCIATE capability, combined with proprietary session tracking that maintains performance even under heavy load. This architecture ensures that the fundamental question of UDP IP vs TCP IP becomes irrelevant—users get the speed of UDP combined with the reliability and legitimacy of static residential infrastructure.
For most applications, UDP proxy configuration follows this general pattern:
Obtain proxy credentials: Ensure the provider explicitly supports UDP (many low-cost providers do not).
Configure SOCKS5 with UDP support: In applications that support it (e.g., gaming clients, custom scripts), specify:
For applications without native UDP proxy support: Use a local tunneling tool like
1socat1redsocksExample using socat for UDP forwarding:
1# Forward UDP traffic from local port 5300 to a remote DNS server via SOCKS5 proxy
2socat UDP-LISTEN:5300,fork SOCKS5:proxy-host:53,socksport=1080
3MTU considerations: UDP proxies should use appropriate Maximum Transmission Unit settings. For residential proxies, setting MTU to 1400 bytes avoids fragmentation across most network paths.
Idle timeout alignment: Match proxy session timeouts to application keepalive intervals. VoIP applications typically send keepalives every 30 seconds; proxy timeouts should exceed this.
Latency benchmarking: Test UDP proxy performance using tools like iperf3 with UDP mode to measure jitter, packet loss, and throughput before production deployment.
The UDP proxy ecosystem represents a sophisticated intersection of network engineering, application requirements, and operational security. As real-time applications continue to dominate internet traffic—from immersive gaming to global video conferencing—the ability to route UDP traffic efficiently, anonymously, and reliably becomes increasingly critical.
Understanding the foundational elements—what is a UDP port, the nuanced tradeoffs in UDP IP vs TCP IP, and the architectural requirements of UDP proxying—empowers professionals to make informed infrastructure decisions.
Related Article: